What Is a Hash Function?
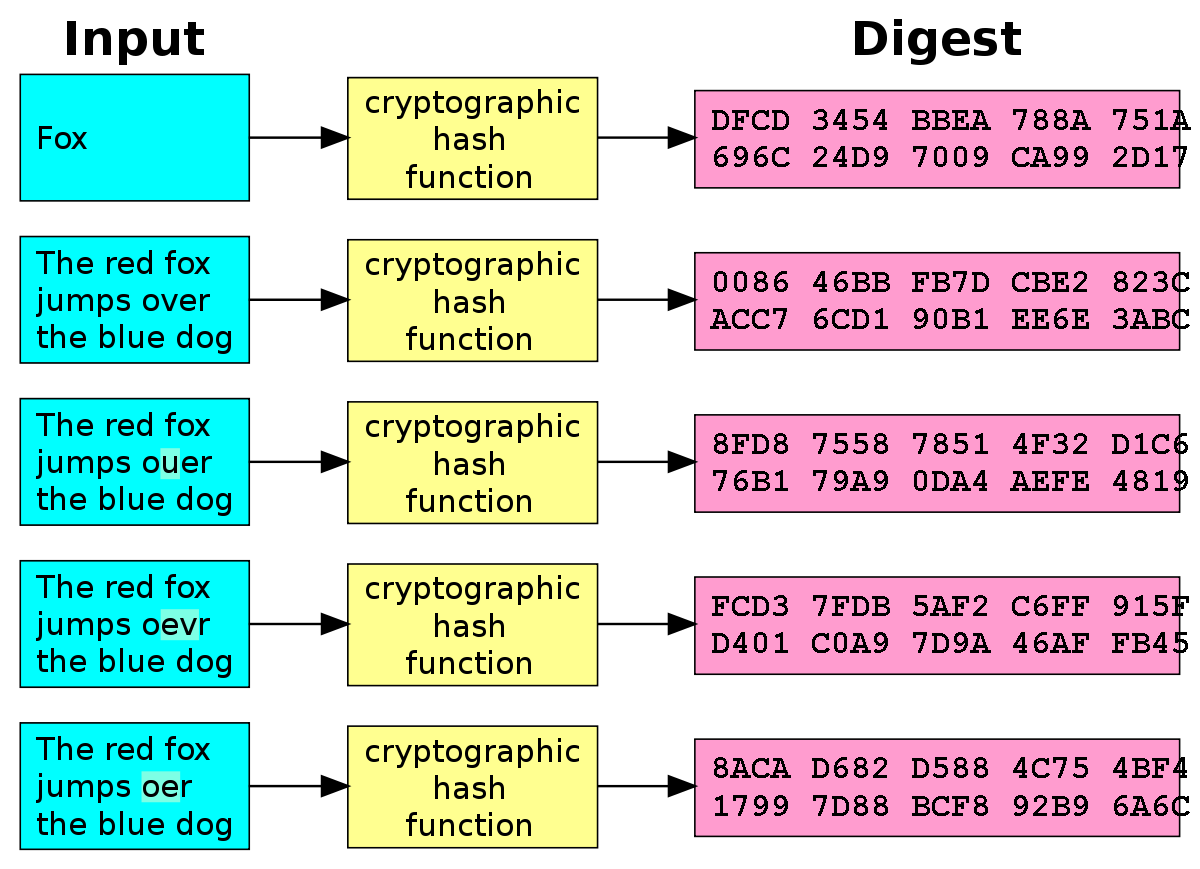
A hash function is a mathematical algorithm that takes an arbitrary input (often a string of data) and produces a fixed-size output known as a hash value or digest. These hash values are typically represented as a sequence of characters (usually hexadecimal digits). Here are some key features of cryptographic hash functions:
- Fixed-Length Output:
- Hash functions convert data of varying lengths into a fixed-length hash value.
- Think of it as compressing information into a compact representation.
- Common hash lengths range from 160 to 512 bits.
- Efficiency:
- Computationally, hash functions are lightning-fast compared to symmetric encryption.
- Given an input
x, computingh(x)(wherehis the hash function) is a swift operation.
Properties of Cryptographic Hash Functions
- Pre-Image Resistance:
- A hash function should make it computationally challenging to reverse-engineer the original input from its hash value.
- In other words, given a hash value
z, finding an inputxsuch thath(x) = zshould be difficult. - This property safeguards against attackers who only possess the hash value and want to find the original input.
- Second Pre-Image Resistance:
- Given an input
xand its hashh(x), it should be hard to find a different inputysuch thath(y) = h(x). - Protects against substitution attacks where an attacker tries to replace a legitimate input with a different one.
- Given an input
- Collision Resistance:
- Hash functions should make it challenging to find two distinct inputs (
xandy) that produce the same hash value (h(x) = h(y)). - While collisions are theoretically possible due to the fixed hash length, a good hash function ensures they are practically hard to find.
- This property is crucial for maintaining data integrity.
- Hash functions should make it challenging to find two distinct inputs (
Applications of Cryptographic Hash Functions
- Password Storage:
- Instead of storing plaintext passwords, systems store their hash values.
- During authentication, the hash of the entered password is compared with the stored hash.
- Data Integrity:
- Hashes verify the integrity of files, ensuring they haven’t been tampered with.
- For example, software downloads often provide hash values for users to verify the authenticity of the downloaded file.
- Digital Signatures:
- Hash functions play a role in creating digital signatures.
- The hash of a message is signed with a private key, providing authenticity and non-repudiation.
- Blockchain and Cryptocurrencies:
- Blockchain relies heavily on hash functions for linking blocks and ensuring data consistency.
- Cryptocurrencies use hash functions for mining and transaction verification.
Conclusion
Cryptographic hash functions are the unsung heroes of cybersecurity. They quietly secure our data, validate transactions, and keep the digital world running smoothly. So next time you encounter a hash value, remember that behind those seemingly random characters lies a robust mathematical foundation!